A cybersecurity compliance audit on the horizon can strike fear in the hearts of company executives, and their IT personnel. And why wouldn’t it be? Most businesses are non-compliant. In fact, in its latest Congressional Budget Justification, the SEC estimates that in 2018, 90% of firms will receive compliance deficiency letters. This number is astounding from a customer perspective: You, as a consumer, can trust almost no organization with your data. But from a company perspective, you are lost in a sea of non-compliant organizations. You’re a needle in a haystack, just hoping the regulators don’t find you.
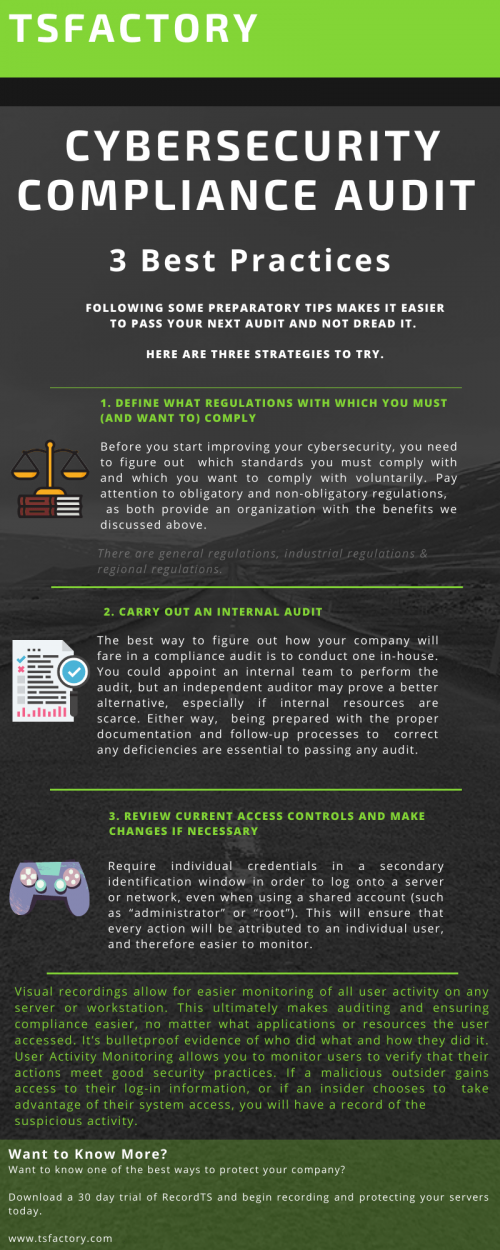
But, following some preparatory tips makes it easier to pass the audit and not dread it. Here are three strategies to try.
1. Define IT regulations with which you must (and want to) comply for your cyber security audit
Before you start improving your cybersecurity, you need to figure out which standards you must comply with and which you want to comply with voluntarily. Pay attention to obligatory and non-obligatory regulations, as both provide an organization with the benefits we discussed above.
For example, companies that handle credit card data must be PCI-DSS compliant, and doing so means having a firewall between a wireless network and the cardholder data repository and using a network detection intrusion system — among other things.
There are three types of regulations:
General regulations apply to a wide list of organizations, regardless of their location or industry. Examples: National Institute of Standards and Technology (NIST) Special Publication 800-53, ISO 27001
Industrial regulations apply to specific industries or organizations that handle specific types of data. Examples: Health Insurance Portability and Accountability Act (HIPAA), Payment Card Industry Data Security Standard (PCI DSS), Sarbanes–Oxley (SOX) act
Regional regulations apply in particular countries, regions, or US states. Examples: EU General Data Protection Regulation (GDPR), UK Data Protection Act, California Consumer Privacy Act (CCPA), New York State Department of Financial Services (NYDFS) Cybersecurity Regulation
2. Carry out an Internal Audit
The best way to figure out how your company will fare in a cybersecurity compliance audit is to conduct one in-house. You could appoint an internal team to perform the audit, but an independent auditor may prove a better alternative, especially if internal resources are scarce. Either way, being prepared with the proper documentation and follow-up processes to correct any deficiencies are essential to passing any audit.
To conduct a self-audit and make it look more like a real audit, use an official IT compliance audit checklist and guidelines:
NIST assessment and auditing resources
GDPR checklist for data controllers
HIPAA compliance checklists
The one big drawback to self-audits is their rather high cost, both in terms of money and time. However, discovering gaps in cybersecurity during an actual audit has an even higher cost: failing the audit and starting over.
3. Review current access controls and make changes if necessary
Require individual credentials in a secondary identification window in order to log onto a server or network, even when using a shared account (such as “administrator” or “root”). This will ensure that every action will be attributed to an individual user, and therefore easier to monitor.
Visual recordings allow for easier monitoring of all user activity on any server or workstation. This ultimately makes auditing and ensuring compliance easier, no matter what applications or resources the user accessed. It’s bulletproof evidence of who did what and how they did it. User Activity Monitoring allows you to monitor users to verify that their actions meet good security practices. If a malicious outsider gains access to their log-in information, or if an insider chooses to take advantage of their system access, you will have a record of the suspicious activity.
Want to Know More?
Want to know one of the best ways to protect your company?
Download a 30 day trial of RecordTS and begin recording and protecting your servers today.