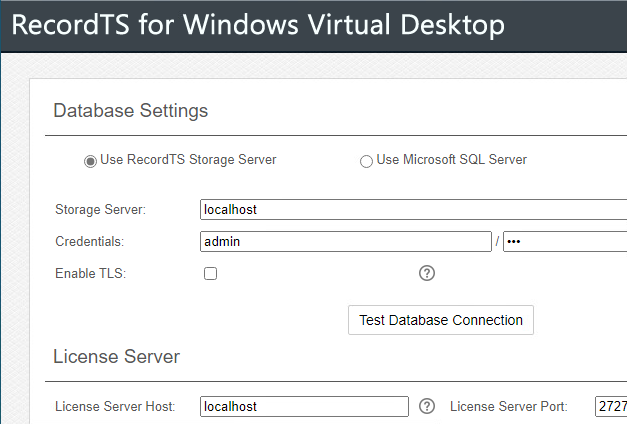
RecordTS v6 now boasts a new recorder designed from the ground up to work with Microsoft Azure Windows Virtual Desktops. It is protocol agnostic and works with any hosting or cloud environment such as Citrix, VMware, AWS, etc. What does protocol agnostic mean? It means that this new recorder does not wedge itself into the […]