It’s nearly the end of Cybersecurity Awareness Month 2021 and TSFactory is highlighting how to prevent phishing attacks. Phishing attacks are one of the most common security challenges that both individuals and companies face in keeping their information secure. Whether it’s getting access to passwords, credit cards, or other sensitive information, hackers are using email, social media, phone calls, and any form of communication they can to steal valuable data. Businesses, of course, are a particularly worthwhile target. Below are important tactics your organization can take to prevent phishing attacks.
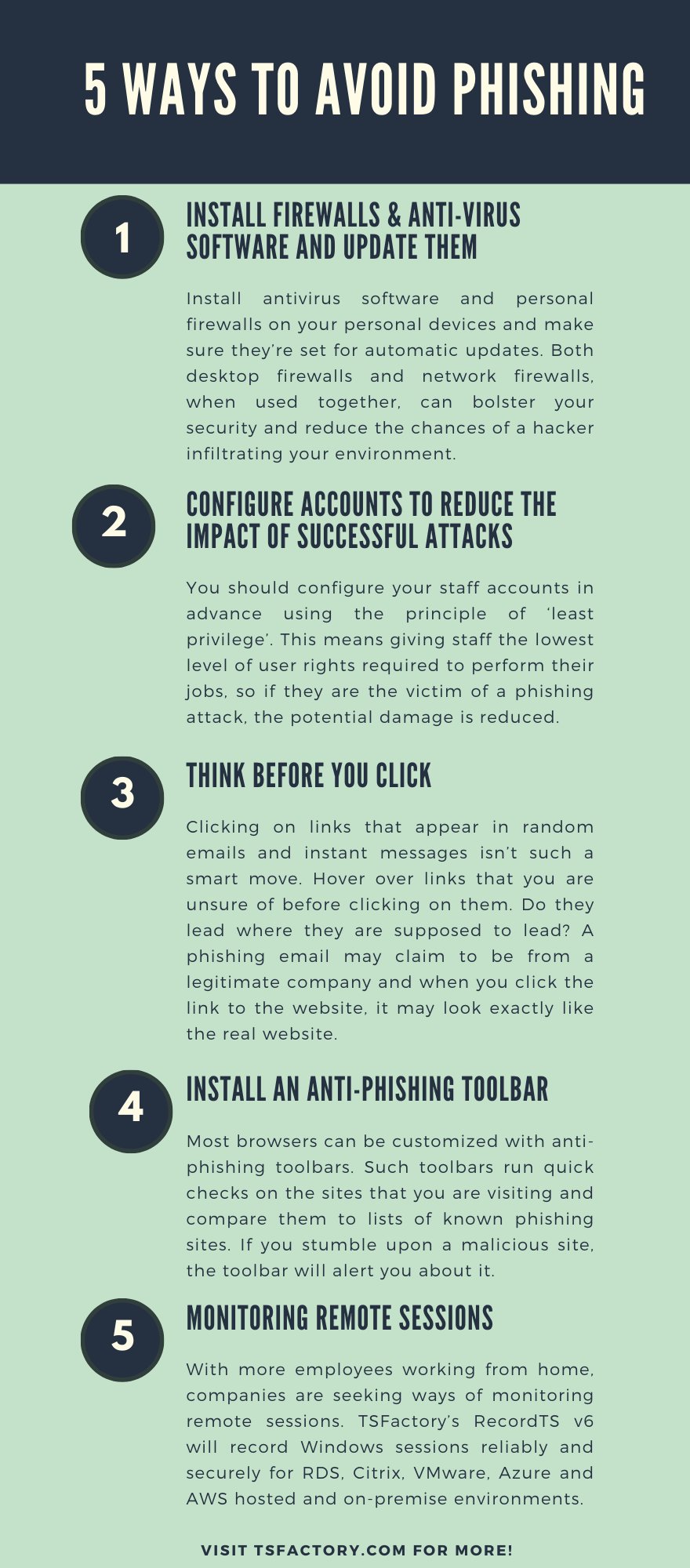
1. Install Firewalls & Anti-virus Software AND Update Them
US-CERT recommends installing antivirus software and personal firewalls on your personal devices and making sure they’re set for automatic updates. Firewalls are an effective way to prevent external attacks, acting as a shield between your computer and an attacker. Both desktop firewalls and network firewalls, when used together, can bolster your security and reduce the chances of a hacker infiltrating your environment.
It’s also essential to keep business and personal use separate — especially if you’re working remotely: don’t use your corporate device out of convenience to browse the internet, online shop, scroll through social media or check personal email.
Receiving numerous update messages can be frustrating, and it can be tempting to put them off or ignore them altogether. Don’t do this. Security patches and updates are released for a reason, most commonly to keep up to date with modern cyber-attack methods by patching holes in security. If you don’t update your browser, you could be at risk of phishing attacks through known vulnerabilities that could have been easily avoided.
2. Configure accounts to reduce the impact of successful attacks
You should configure your staff accounts in advance using the principle of ‘least privilege’. This means giving staff the lowest level of user rights required to perform their jobs, so if they are the victim of a phishing attack, the potential damage is reduced. To further reduce the damage that can be done by malware or loss of login details, ensure that your staff don’t browse the web or check emails from an account with Administrator privileges. An Administrator account is a user account that allows you to make changes that will affect other users. Administrators can change security settings, install software and hardware, and access all files on the computer. So an attacker having unauthorised access to an Administrator account can be far more damaging than accessing a standard user account.
Use two-factor authentication (2FA) on your important accounts such as email. This means that even if an attacker knows your passwords, they still won’t be able to access that account.
3. Think Before You Click
It’s fine to click on links when you’re on trusted sites. Clicking on links that appear in random emails and instant messages, however, isn’t such a smart move. Hover over links that you are unsure of before clicking on them. Do they lead where they are supposed to lead? A phishing email may claim to be from a legitimate company and when you click the link to the website, it may look exactly like the real website. The email may ask you to fill in the information but the email may not contain your name. Most phishing emails will start with “Dear Customer” so you should be alert when you come across these emails. When in doubt, go directly to the source rather than clicking a potentially dangerous link.
4. Install an Anti-Phishing Toolbar
Most browsers can be customized with anti-phishing toolbars. Such toolbars run quick checks on the sites that you are visiting and compare them to lists of known phishing sites. If you stumble upon a malicious site, the toolbar will alert you about it. This is just one more layer of protection against phishing scams, and it is completely free.
Some of these programs are completely free, while others require paying a minimal fee, before downloading what is a fairly lightweight client. This software is then ready to help you detect phishing sites, running unnoticed in the background at all times.
Anti-phishing toolbars are useful, as they check everything that you may click on in real-time, blocking anything that could possibly be malicious. This is useful for those who aren’t particularly technologically savvy. But there is a downside to this technology as well.
The fact that toolbars are generally free to download, is not exactly an indication of quality and research has also indicated that this approach to phishing has a relatively low success rate.
Certainly, toolbars shouldn’t be viewed as comprehensive anti-phishing coverage. Even if they can be a nifty and useful tool in some circumstances.
5. Cloud-Based Anti-Phishing
Another aspect of cloud-phishing tools that is worth considering are cloud-based solutions. These are focused on a wide range of potential avenues for phishing attacks, but often particularly help protect email from attackers.
Cloud-based solutions can be updated on a very regular basis, due to the way that the cloud operates, while cloud-based solutions are also convenient, as they can be built into a cloud package at the retail level.
Cloud-based anti-phishing tools aren’t necessarily more sophisticated than other forms of anti–phishing software. But they are more flexible and adaptable, while being able to incorporate the information generated by the experiences of many users.
Tapping into the power of the cloud helps anti-phishing work in an almost automated fashion, complementing other techniques and strategies.
6. Monitoring Remote Sessions
With more employees working from home, companies are seeking ways of monitoring remote sessions. One compelling case can be made for recording remote sessions for later playback and review. Employers are concerned that in the event of a security breach, they won’t be able to see what was happening on users’ desktops when the breach occurred. Another reason for recording remote sessions is to maintain compliance, as required for medical and financial institutions or auditing for business protocols, etc.
TSFactory’s RecordTS v6 will record Windows sessions reliably and securely for RDS, Citrix, VMware, Azure and AWS hosted and on-premise environments. Scalable from small offices with one server to enterprise networks with tens of thousands of desktops and servers, RecordTS integrates seamlessly with the native environment.
Click here to learn more about secure remote session recording.
References
https://digitalguardian.com/blog/phishing-attack-prevention-how-identify-avoid-phishing-scams
https://www.lepide.com/blog/10-ways-to-prevent-phishing-attacks/
https://www.wired.com/2017/03/phishing-scams-fool-even-tech-nerds-heres-avoid/
https://www.cyberark.com/resources/blog/8-ways-to-fight-the-phish-this-cybersecurity-awareness-month
https://www.ncsc.gov.uk/collection/small-business-guide/avoiding-phishing-attacks
https://www.phishing.org/10-ways-to-avoid-phishing-scams
https://pixm.net/blog/phishing-attacks/anti-phishing-tools/