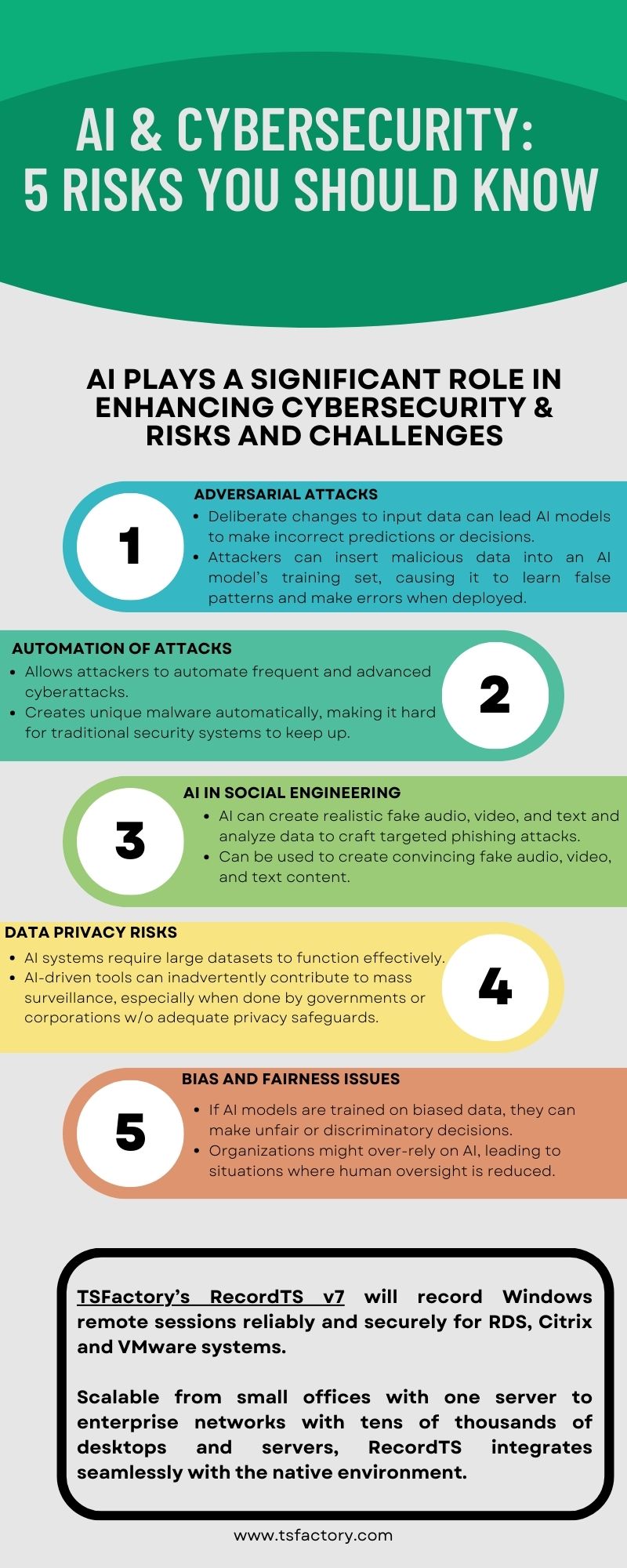
Cybersecurity threats are evolving, and one of the most concerning developments is the use of AI in social engineering attacks. One such attack is vishing—a form of phishing that occurs over voice communication. With AI-powered voice synthesis and deepfake technology, cybercriminals are now executing vishing attacks that are more sophisticated and convincing than ever before. […]